
Why use k3s?
k3s is a lightweight Kubernetes distribution designed to be minimal and efficient, making it well-suited for resource-constrained environments and use cases where simplicity and ease of deployment are important. It was created by Rancher Labs and is intended to simplify the installation and management of Kubernetes clusters.
In this example use k3s with Traefik ingress controller so it’s a default by K3s and it’s a lightweight, easy, and fast solution, but if you prefer another one feel free to use it.
Why use cert manager?
Using cert-manager on Kubernetes simplifies SSL/TLS certificate management, automates the renewal process, integrates seamlessly with Kubernetes resources, and provides the flexibility to work with various certificate issuers. This results in enhanced security and reduced operational overhead for securing your Kubernetes applications.
1. Install k3s
| |
If you want to have access to the k3s cluster outside the node, you can use the following parameter when creating the cluster --tls-san.
| |
By default, you do not have to execute permissions on k3.conf to resolve you need to move the file and give it the necessary permissions.
NOTE : It’s not recommended to give permissions to the original file.
| |
You can add
KUBECONFIG=~/.kube/configto your~/.profileor~/.bashrcto make it persist on reboot.
2. Install helm (optional)
This step is completely optional in order to follow the tutorial but highly recommended.
Helm is a package manager for Kubernetes that simplifies the deployment and management of applications in Kubernetes clusters.
Install Helm on K3s is really easy, just execute the script and you don’t need to modify any config !
| |
3. Install cert manager
Mainly, we have two ways to install with helm or with kubectl. Personally I prefer to use the helm package manager with all the advantages that comes with it.
Option 1: Install by Helm (recommended)
Add the oficial repository on Helm
| |
Update your local Helm chart repository
| |
And install de cert-manager with namespace cert-manager
| |
NOTE : You can find the all config parameters on the oficial chart page: https://artifacthub.io/packages/helm/cert-manager/cert-manager
Option 2: Install by kubectl
| |
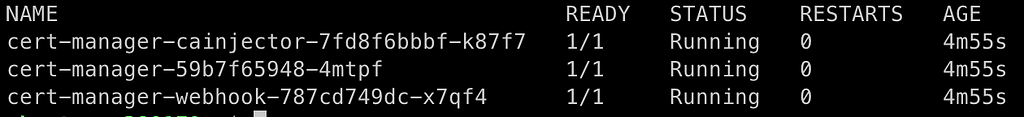
3.1 Verify the cert manager installation
| |
4. Create the ClusterIssuer resource
Create ClusterIssuer for staging environment
| |
| |
Create ClusterIssuer for production environment
| |
| |
Verify that it has been properly applied
| |
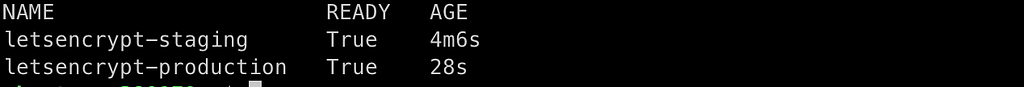
And check the status of ClusterIssuer
| |
5. Let’s play!
Finally we are going to create our certificate
5.1 Create a dummy application
In this step just create a very basic dummy nginx application, if you already have an application you can go to the next step.
Create a deployment using a default image from nginx:alpine
| |
Show the deployments status
| |
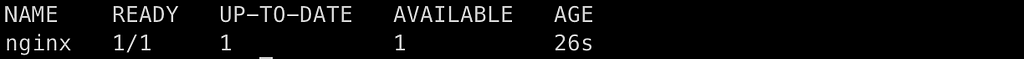
| |
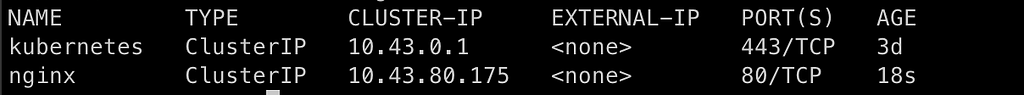
Expose the server at port 80
| |
Check that the service is correct and running
| |
5.2 Create a ingress traefik controller
Define the trafik ingress with the cert-manager annotations and the tsl section to be able to manage our certificate.
| |
| |
Verify that the certificate has actually been created
| |
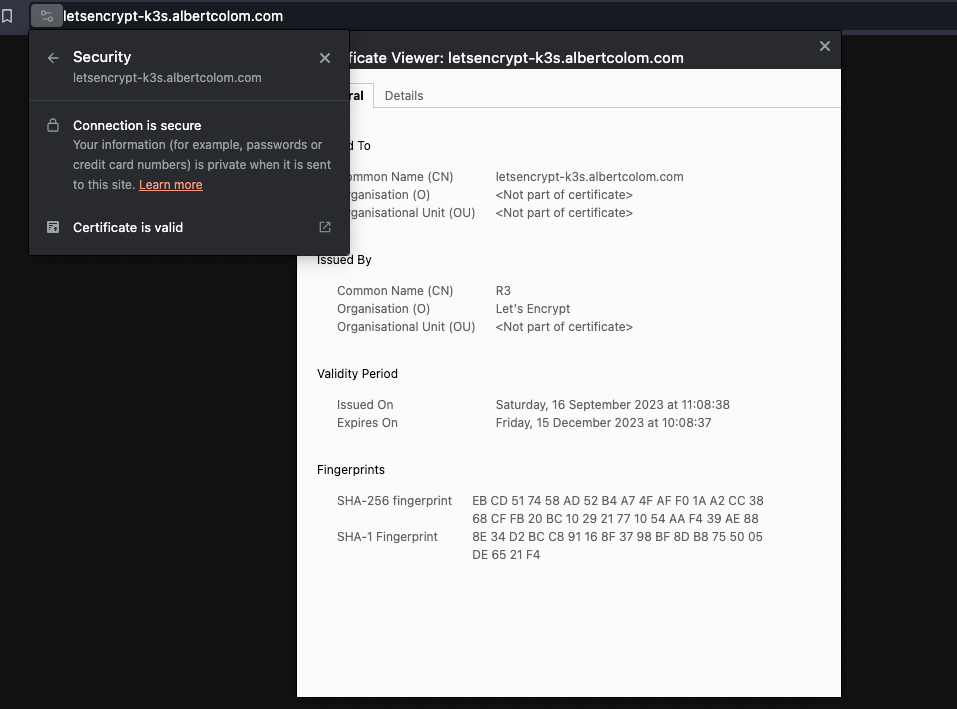
NOTE : I change the host
example.comto letsencrypt-k3s.albertcolom.com and changeexample-com-tlsto letsencryptk3s-albertcolom-com-tls .

You can show the valid certificated by Let’s Encrypt!
Conclusion
Once you have installed cert manager it is really easy to manage your certificates together with traefik. You just have to set a couple of parameters in the ingress and the system takes care of everything.
No more excuses for not using a valid certificate!
You can read the article on Medium